Secure hosting
Reliability, data security, scalability, system maintenance and simple/fast deployment are the basis for a secure and reliable remote maintenance solution.
The Netbiter Argos platform is based on years of experience and delivers what it promises.
The Netbiter Argos servers are operated in a professional environment that is specially designed for this purpose.
This includes multiple systems that are maintained and operated at geographically diverse locations by well-trained personnel.

Our hosting concept
- Round-the-clock monitoring of server availability (24/7)
- Multiple servers at different locations
- Multiple data storage locations
- Theft protection
- Fire alarm systems
- Double data backup at different locations
- Redundant Internet access from different providers
- Emergency power generators
Measures for the security of your data
Netbiter is also used in business-critical applications - trust, reliability, encryption and compliance with the highest standards are central aspects of the Netbiter remote maintenance solution.
Some of the security features of Netbiter Argos:
- On-site network security (broadband Internet access)
The architecture of the Netbiter data portal enables existing security infrastructure to be retained. A special communication procedure between the Netbiter Gateways and the Argos data portal enables data exchange even across firewalls. This procedure is generally approved by the internal IT departments and guarantees the security of the installation. - Network security at the site (Wireless GPRS)
To ensure secure communication via GPRS, we offer SIM cards for exclusive use with the Netbiter solution. This also means that it is not possible to ping or gain access to the remote site except via the Netbiter Argos data portal. This also reduces unnecessary and costly GPRS data traffic.
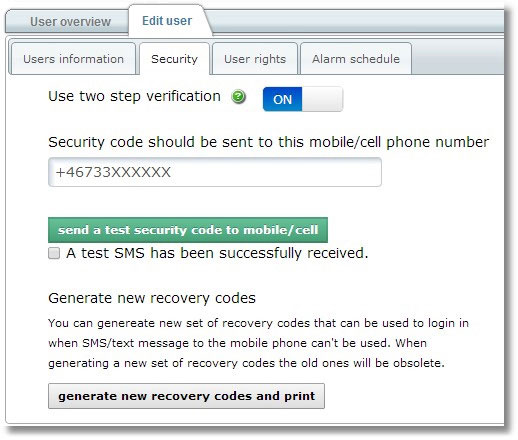
- User authentication (2-stage)
All access to www.netbiter.net requires the entry of a user name and password. User rights can be assigned to grant or deny access to certain functions. Two-stage authentication is also possible. In this case, the user must enter a one-time access code that is sent to their cell phone/smartphone. This 2-step authentication is optional and can be configured for each user. - Separate data areas for users
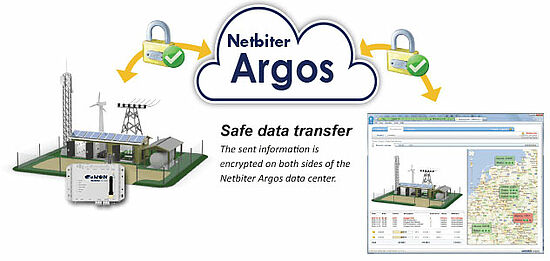
User management ensures that users can only access the data for which they are responsible. - Secure data communication
All data communication is encrypted using Secure Socket Layer (SSL). Banks use the same method for secure online transactions.



